Recognizing Online Manipulation Tactics
Ah, the world of online manipulation tactics – a digital battleground where deception lurks behind every click and keystroke. In this vast cyber realm, nefarious individuals and entities employ a myriad of cunning strategies to sway opinions, extract personal information, and sow discord among unsuspecting netizens.
Picture this: you’re scrolling through your social media feed when suddenly you come across a too-good-to-be-true offer that promises to solve all your problems with a simple click. Before you hit that enticing button, pause and remember the wise words of tech entrepreneur Jaron Lanier, who once said, “When you challenge the motives of people using the internet, the first thing they do is imply that you’re inauthentic, that you’re flattering yourself by thinking you could be virtuous.” Yes, my friends, online manipulators often rely on flattery and false promises to lure you into their web of deceit. Be vigilant for exaggerated claims, overly emotional appeals, and requests for personal information out of the blue – these are telltale signs of a digital con artist at work.
Building Trust with Caution
Trust is like a delicate flower in the online world – one wrong move and it withers away faster than you can say “password123.” In our digital age, building trust with caution is paramount to safeguarding your personal information from the lurking threat of cyber predators. It’s a bit like dating in the cyber realm – take it slow, keep your guard up, and don’t give away your heart (or your social security number) too soon.
When navigating the vast seas of the internet, it’s essential to remember that not everyone is who they claim to be. As renowned cybersecurity expert Kevin Mitnick once said, “The weakest link in the security chain is the human element.” So, before laying all your cards on the virtual table, take a step back, squint your eyes, and give that suspicious email or dubious website a good ol’ side-eye. Trust me, a healthy dose of skepticism can go a long way in this digital jungle.
Spotting Red Flags in Online Communication
When it comes to navigating the vast sea of online communication, spotting red flags is like having a trusty compass to guide you through murky waters. One of the first things to keep an eye out for is overly vague messages that lack specificity. If someone is being evasive or dodging direct questions like a skilled politician, it might be time to raise an eyebrow and proceed with caution. As the great Maya Angelou once said, “When someone shows you who they are, believe them the first time.”
Another red flag to watch for is the speed at which a conversation escalates. Just like a pot of water reaching its boiling point, if someone is pushing for rapid intimacy or asking for personal information too soon, it’s crucial to hit the brakes. Remember the wise words of Benjamin Franklin, “Three may keep a secret, if two of them are dead.” Privacy is not something to take lightly in the digital age, so guard your personal information as fiercely as a dragon protects its hoard of treasure.
Protecting Personal Information Online
As we navigate the vast digital landscape, safeguarding our personal information is akin to protecting a prized possession in a virtual world filled with lurking cyber adversaries. The online realm, much like a bustling metropolis, teems with requests for our data, each one vying for a piece of our digital identity like a crew of seagulls eyeing a dropped ice cream cone at the beach. It’s essential to approach this virtual circus with a discerning eye and a cloak of digital invisibility, like a modern-day digital ninja vanishing into the shadows of the cyber realm.
In this age of rampant data breaches and online snooping, one must don the armor of encryption and wield the sword of privacy rights to fend off the prying eyes of data thieves and cyber miscreants. As the renowned cryptographer Whitfield Diffie once said, “Privacy is necessary for an open society in the electronic age.” So, let us band together in this digital frontier, championing the cause of privacy and encryption like noble warriors in a quest to safeguard our digital sovereignty. Remember, in the online realm, your personal information is your most valuable currency so guard it with the vigilance of a dragon hoarding its treasure in a far-off mountain cave.
And as we navigate the treacherous waters of the digital world, let us remember that in the battle for privacy and security, knowledge truly is power. So, arm yourself with awareness, fortify your defenses with encryption, and above all, trust your instincts in the vast cyber wilderness. After all, in the immortal words of Albert Einstein, “The world is a dangerous place to live; not because of the people who are evil, but because of the people who don’t do anything about it.” So, let us rise to the challenge, taking a stand for our digital rights and protecting our personal information with all the fervor of a true cyber champion.
Understanding the Psychology Behind Manipulation
Manipulation is a crafty dance of influence, a psychological game where the manipulator seeks to bend the will of their target to suit their desires. In the realm of online interactions, understanding the psychology behind manipulation is paramount in safeguarding oneself against falling prey to such tactics. As the eminent psychologist Robert Cialdini once said, “The most potent weapon of the oppressor is the mind of the oppressed.” Manipulators tap into cognitive biases and emotional triggers, subtly weaving a web of influence that can be hard to detect until it’s too late.
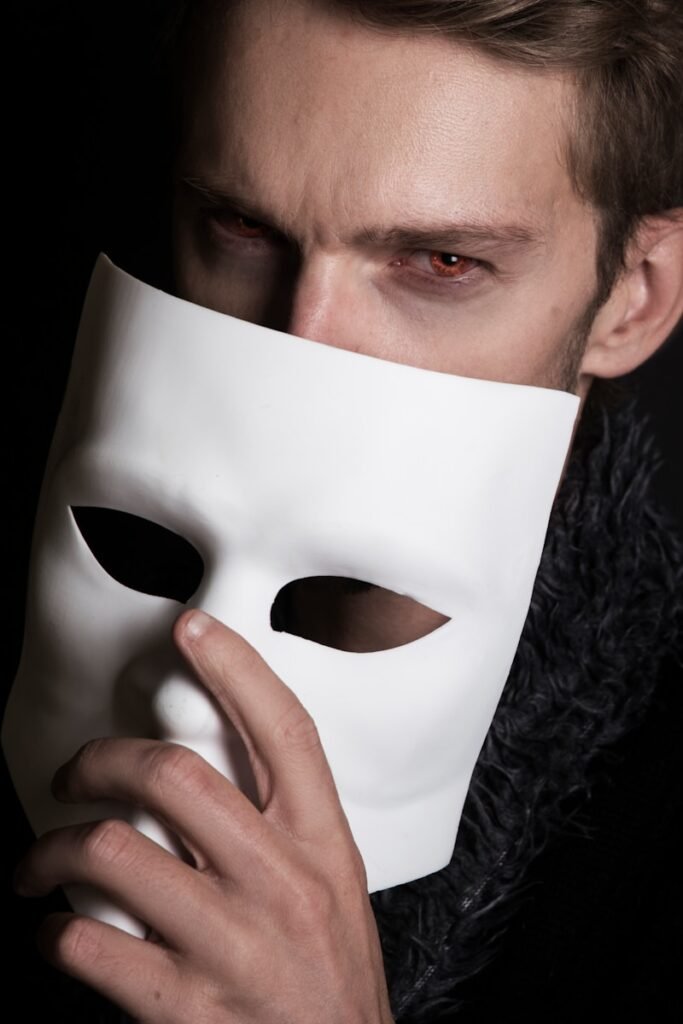
Moreover, in the digital landscape, where screens serve as shields and avatars as masks, the art of manipulation takes on a new guise. The anonymity provided by the internet opens the floodgates for individuals to craft personas that may not align with their true selves. This creates a breeding ground for manipulation to flourish, as people can easily deceive and manipulate others without the constraints of face-to-face interactions. In the words of Carl Sagan, “One of the saddest lessons of history is this: If we’ve been bamboozled long enough, we tend to reject any evidence of the bamboozle. We’re no longer interested in finding out the truth.”
Falling Victim to Online Scams
In the whimsical world of online scams, it can be all too easy to fall down the rabbit hole of deception. From too-good-to-be-true investment opportunities promising instant riches to emails declaring you’ve won a lottery you never even entered, the internet is a playground for scammers with a knack for preying on the unsuspecting. As the wise Richard Branson once said, “The key to success is to focus our conscious mind on things we desire not things we fear.”
One moment you’re leisurely scrolling through your inbox, and the next, you’re on the brink of wiring money to a Nigerian prince in desperate need of your assistance. It’s a treacherous digital dance where the promise of easy money or unbelievable bargains often leads straight into the jaws of cybercriminals. As Benjamin Franklin astutely remarked, “An investment in knowledge pays the best interest.” So, arm yourself with awareness and a healthy dose of skepticism to sidestep the pitfalls of online deceit.
Guarding Against Emotional Manipulation
Emotional manipulation can be as sneaky as a spy trying to infiltrate your circle of trust online. It’s like when you receive a message from a stranger claiming to be a long-lost relative in need of urgent financial help – it tugs at your heartstrings, but beware, it might just be a crook trying to pull a fast one on you. Remember, just because someone seems friendly and sympathetic doesn’t mean they have your best interests at heart. When in doubt, take a step back, assess the situation, and never feel pressured to give in to emotional crcion.
In the vast sea of online interactions, it’s crucial to keep your emotional guard up. As cybersecurity guru Kevin Mitnick once said, “Social engineering has become about 75% of an average hacker’s toolkit.” Don’t let your emotions cloud your judgment when you’re met with unexpected requests or sob stories from strangers. Trust your instincts and don’t hesitate to verify the authenticity of the person reaching out to you. Remember, in the realm of emotional manipulation, caution is your best ally.
Strategies for Dealing with Manipulative Behavior
Dealing with manipulative behavior online can be a tricky dance, but fear not, dear reader, for there are ways to outsmart even the most cunning of digital tricksters. One key tactic is to keep your wits about you – don’t fall prey to their smooth talk and false promises. Remember the wise words of Joseph Joubert, “The aim of an argument or discussion should not be victory, but progress.” Stay focused on the goal of the interaction and don’t let yourself be swayed by emotional manipulations or empty flattery.
Another strategy to combat online manipulators is to set clear boundaries and stick to them like glue. As the great Maya Angelou once said, “I’ve learned that you shouldn’t go through life with a catchers mitt on both hands; you need to be able to throw something back.” Don’t let others push you around or guilt-trip you into doing things that make you uncomfortable. Trust your instincts and if something doesn’t feel right, don’t be afraid to speak up and protect your own interests. Remember, in the digital world, just as in the real world, you have the power to control your own narrative.